The Payment Card Industry Security Standards Council has released a bulletin regarding the use of SSL for data protection on the Internet. In the bulletin, the Council states that SSL – a protocol for providing secure communications – is no longer acceptable for secure transactions. This has left many people wondering what the implications are for consumer purchases over the web.
The Council
 First, a quick look at what exactly the PCI Security Standards Council is. The Council, as it is often referred to, was founded by American Express, Discover Financial Services, JCB International, MasterCard, and Visa. The purpose of the Council is to not only develop but also to maintain and manage payment card security standards.
First, a quick look at what exactly the PCI Security Standards Council is. The Council, as it is often referred to, was founded by American Express, Discover Financial Services, JCB International, MasterCard, and Visa. The purpose of the Council is to not only develop but also to maintain and manage payment card security standards.
Our standards cover everything from the point of entry of card data into a system, to how the data is processed, through secure payment applications. We seek to protect and educate industry players such as merchants, processors, financial institutions, and any other organizations that store, process, and transmit cardholder data, around the world.
While the Council does not validate or enforce an organization’s compliance, merchants with questions about compliance can bring them up with one of the founding payment brands, so the Council does indeed carry quite a bit of weight when it comes to establishing payment card security standards.
As mentioned above, the main component of the Council’s bulletin is this (emphasis added):
To ensure the continued strength and integrity of PCI Standards for payment data protection, the Council has ongoing processes for monitoring threats and vulnerabilities and for updating the standards as necessary. The National Institute of Standards and Technology (NIST) has identified the Secure Socket Layers (SSL) v3.0 protocol (a cryptographic protocol designed to provide secure communications over a computer network) as no longer being acceptable for protection of data due to inherent weaknesses within the protocol. Because of these weaknesses, no version of SSL meets PCI SSC’s definition of “strong cryptography,” and revisions to the PCI Data Security Standard (PCI DSS) and the Payment Application Data Security Standard (PA-DSS) are necessary.
For the non-technical, that can sound like a lot of mumbo-jumbo and lead to confusion and misinterpretation on what exactly the Council is saying. To start understanding this, we need to understand exactly what SSL is.
What is SSL?
Whenever you connect to a website and your browser shows either a lock icon or “HTTPS” at the beginning of the URL, you are using a secure HTTP connection. The secure connection encrypts the data that you send from your computer to the website server your are visiting so that only your computer and the server can access that information, and is very important when making any type of online purchase or when you are entering personal information or logging into websites. This secure HTTP connection is built using the SSL/TLS protocol family. The confusion with secure HTTP connections is not the connection itself, but in that in most circles the term SSL is used to mean any type of secure connection, and this isn’t the case. In fact, HTTPS is built on top of either the SSL or TLS protocol.
Without getting too technical, simply put SSL was the name given to the first versions of the security protocol and was first released by Netscape in 1995. In 1996, SSL was updated to version 3. As you can see, this means that SSL is a fairly old security protocol.
TLS – transport layer security – arrived in 1999 as an upgrade of SSL 3. TLS 1.01 was defined in 2006, and TLS 1.2 in 2008. Currently TLS 1.3 is in draft mode.
So to summarize, SSL is NOT a blanket term for secure Internet communications but rather a specific protocol used to secure your Internet traffic that has already been mostly replaced with the newer – and more secure – TLS protocol.
The Bulletin
So what does the bulletin provided by the Council mean? Now that you know exactly what SSL is, and what it refers to, the bulletin shouldn’t be as alarming as it first seems.
Because of these weaknesses, no version of SSL meets PCI SSC’s definition of “strong cryptography,” and revisions to the PCI Data Security Standard (PCI DSS) and the Payment Application Data Security Standard (PA-DSS) are necessary.
Yes SSL is no longer secure as a communication protocol, and yes the Council is updating its standards, and yes it is recommending that organizations and IT departments assess if they are still using SSL and determine their options for upgrading to a proper, more secure protocol (like TLS) – and that’s a GOOD thing.
In a nutshell, any website processing payment card transactions will no longer be permitted to encrypt online payment transactions using the SSL protocol.
What does this mean for you?
In all honesty, as a consumer this means almost nothing for you. TLS has been around for awhile and has been replacing SSL on many servers. The only browser/operating system combination that doesn’t support TLS is IE 6 on Windows XP, and if you’re still using a combination of those you need to speak to your IT department or upgrade your personal computer yesterday as Windows XP is no longer supported as an operating system. So, in practice virtually every server supports TLS connections. Because most browsers support TLS, then almost all sessions will be secured using the TLS protocol.
Web browser developers have been proactive as well in limiting use of the SSL protocol and have all disabled SSL 3 and SSL 3 fallback (allowing their browsers to use SSL if the web server doesn’t support TLS) in their latest versions.
- Chrome: disabled SSLv3-fallback in Chrome 39, and disabled SSL3 completely in Chrome 40 (Jan 2015)
- Firefox: disabled SSLv3 in Version 34 (Dec 2014)
- Internet Explorer: SSL 3.0 fallback disabled by default in IE 11 (Feb 2015)
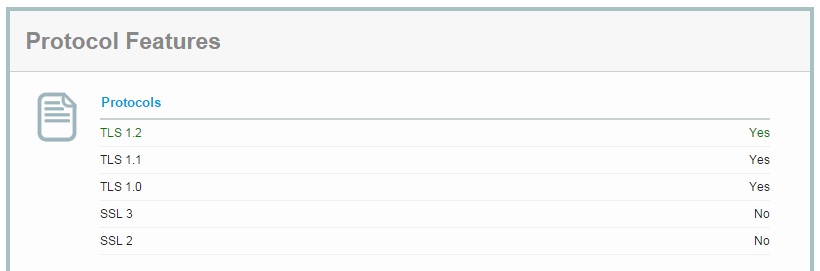
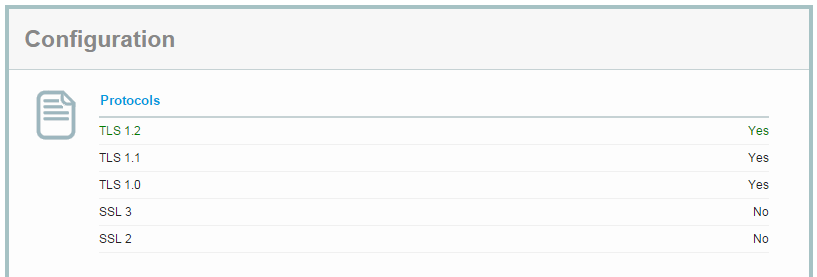
You can also check the SSL/TLS capabilities of your browser at the Qualys SSL Labs website – if you see SSL 3 and SSL 2 set to no in the Protocol Features section, you’re good to go.
If your browser doesn’t support SSL, and it shouldn’t, and you access a website that does not support TLS, then the connection should fail and you won’t be able to access the website. The fact of the matter though is that TLS has been around for 15 years and most websites that take online payments use TLS and only fall back to SSL for browsers that don’t support TLS (IE 6 on Windows XP) – if they fall back at all. For example, if you try to access Amazon.com using IE 6/XP, you’ll get an error message; accessing the site with any other browser will use the latest TLS version (1.0, 1.1, or 1.2) that your browser supports. For the technically inclined, you can see over at Qualys SSL Labs that Amazon doesn’t have SSL implemented on their server, only TLS.
Summary
Hopefully that makes things more clear for you in regards to SSL and secure communications on the Internet. While the Council bulletin sounds dire, once you understand the differences between SSL the protocol and ‘SSL’ as the term is often used in everyday speech, the bulletin isn’t as bad as it sounds and is in fact a great step forward for stronger security while using and making purchases on the Internet.
[button link=”http://training.pcisecuritystandards.org/pci-ssc-bulletin-on-impending-revisions-to-pci-dss-pa-dss-assessor” icon=”fa-external-link” side=”left” target=”blank” color=”285b5e” textcolor=”ffffff”]Source: PCI[/button][button link=”http://en.wikipedia.org/wiki/Transport_Layer_Security#SSL_1.0.2C_2.0_and_3.0″ icon=”fa-external-link” side=”left” target=”blank” color=”285b5e” textcolor=”ffffff”]Source: Wikipedia[/button][button link=”http://tools.ietf.org/html/rfc2246″ icon=”fa-external-link” side=”left” target=”blank” color=”285b5e” textcolor=”ffffff”]Source: TLS Protocol V1 RFC[/button]Last Updated on November 27, 2018.











Comments are closed.