It’s been a rough week for macOS malware. We saw a pretty shady Remote Administration Tool just the other day, and now we’ve learned of a fun new ransomware for Apple’s desktop operating system. Patcher ransomware encrypts your macOS device, though the way it is coded leaves no way for anybody to ever unlock your files. Ever. Just to nip any unnecessary worrying in the bud, as long as you aren’t using torrents to illegally download software you should be fine.
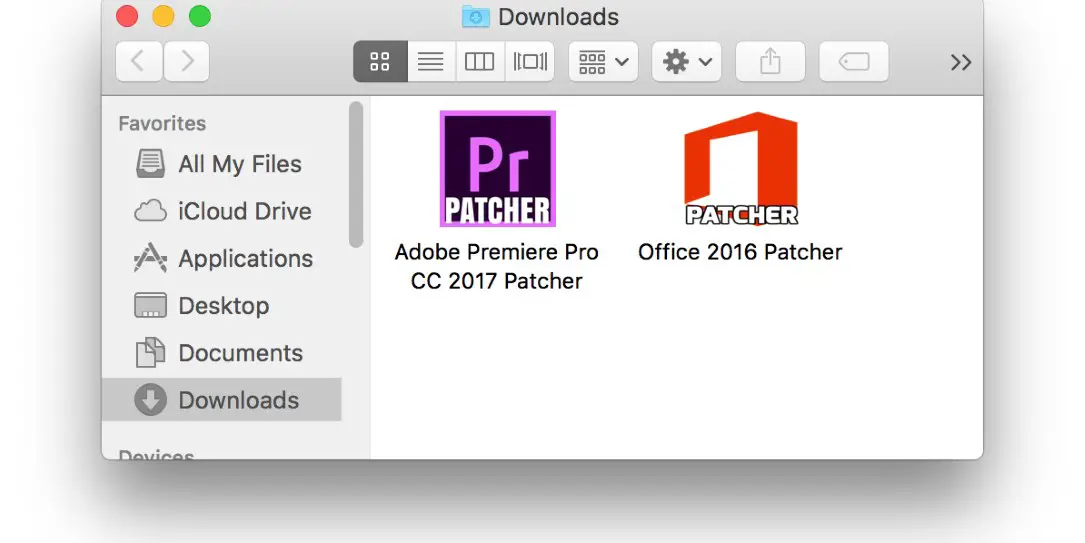
Researchers at ESET discovered the crypto-ransomware early last week, and as the name might imply, Patcher is disguised as an application to crack or patch applications without paying for them. The zipped directory that they found contained files purporting to be patches for Adobe Premiere Pro CC 2017 and Office 2016, though they admitted that other Patcher files could be out in the wild. ESET dove into the code for the ransomware and found it to be, well, sloppy. When opened, the app has a transparent background, which looks bad and can potentially be confusing, and it closed, the window cannot be reopened. The transparent window has a simple “Start” button, which if pressed starts the encryption process.

The ransomware generates a random 25 character string to encrypt your files. The files are zipped into an encrypted archive, at which point the original files are deleted, and the modified time for each archive is set to February 13, 2010 for some unknown reason. The ransomware will move from local accounts to any storage mounted to your system. There is code included that is meant to null any free space on your system, but it is coded incorrectly, so that part won’t run properly.
A Readme!.txt file is copied to various locations across your drive while the encryption is going on, which is hard coded into the file. This means that the instructions, Bitcoin address, and email address are the same for anyone afflicted by this malware. Even more surprising, the email address is provided by Mailinator, which provides a public inbox for anyone without registering or signing in, meaning anybody can view the mailbox associated with this malware. ESET has kept an eye on it and so far they haven’t seen any messages come through, though they admit that any messages could have been quickly deleted before they could see anything.
Thankfully, however, there have been no transactions at the Bitcoin address provided either, meaning the authors haven’t gotten a penny from any unsuspecting users. That’s definitely a good thing because even if a user paid the ransom, the authors wouldn’t be able to unlock the encryption anyway. As ESET discovered:
There is one big problem with this ransomware: it doesn’t have any code to communicate with any C&C server. This means that there is no way the key that was used to encrypt the files can be sent to the malware operators.
This also means that there is no way for them to provide a way to decrypt a victim’s files. Paying the ransom in this case will not bring you back your files. That’s one of the reasons we advise that victims never pay the ransom when hit by ransomware.
Alas, the random ZIP password is generated with arc4random_uniform which is considered a secure random number generator. The key is also too long to brute force in a reasonable amount of time.
As I mentioned at the beginning, as long as you aren’t downloading software from torrent or other sites you should be fine. Though if you’re the type that’s going to download shady things from shady places, just be careful. Even if it weren’t a poorly coded disaster, recovering your system from ransomware can’t be anybody’s idea of a good time.
What do you think about the Patcher ransomware? Is anybody going to fall for this? Let us know in the comment section below, or on Google+, Facebook, or Twitter.
[button link=”http://www.welivesecurity.com/2017/02/22/new-crypto-ransomware-hits-macos/” icon=”fa-external-link” side=”left” target=”blank” color=”285b5e” textcolor=”ffffff”]Source: ESET[/button]









Comments are closed.