Recently an Android vulnerability dubbed “Stagefright” was shown to affect pretty much every Android phone in service. Google moved as quickly as possible to fix the vulnerability with some OEMs promising to make security patches priority one. Most Google Nexus phones should have already received the latest Android security patch but now there’s a report indicating that the patch itself is flawed. Security firm Exodus Intelligence says that the patch Google has pushed to its Nexus devices and has offered up to OEMs has a flaw that allowed them to bypass the patch. Exodus Intelligence has said they’ve notified Google of the flaw in the new patch but have not heard anything back from them. In a blog post Exodus laid out some of what it found.
We notified Google of the issue on August 7th but have not had a reply to our query regarding their release of an updated fix. Due to this, as well as the following facts, we have decided to notify the public of our findings here on the Exodus Intelligence blog.
- The flaw was initially reported over 120 days ago to Google, which exceeds even their own 90-day disclosure deadline.
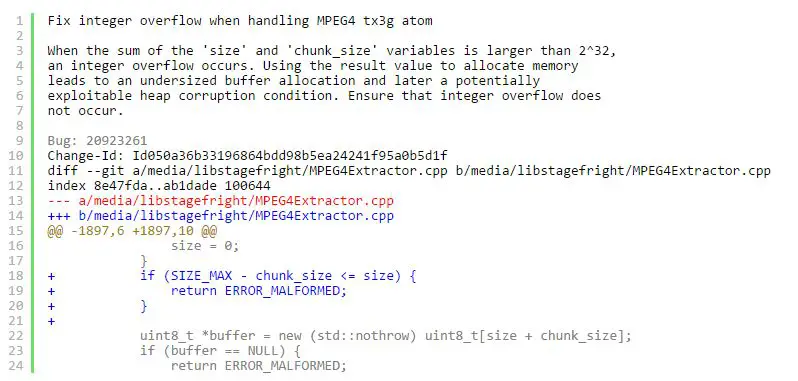
- The patch is 4 lines of code and was (presumably) reviewed by Google engineers prior to shipping. The public at large believes the current patch protects them when it in fact does not.
- The flaw affects an estimated 950 million Google customers.
- Despite our notification (and their confirmation), Google is still currently distributing the faulty patch to Android devices via OTA updates.
- There has been an inordinate amount of attention drawn to the bug–we believe we are likely not the only ones to have noticed it is flawed. Others may have malicious intentions.
- Google has not given us any indication of a timeline for correcting the faulty patch, despite our queries.
- The Stagefright Detector application released by Zimperium (the company behind the initial discovery) reports “Congratulations! Your device is not affected by vulnerabilities in Stagefright!” when in fact it is, leading to a false sense of security among users.
For now we still think the majority of users are safe as there have been no major exploits of the vulnerability and we’re hoping for a quick and solid solution from Google to the issue.
[button link=”http://www.bbc.com/news/technology-33914826″ icon=”fa-external-link” side=”left” target=”blank” color=”285b5e” textcolor=”ffffff”]Source: BBC[/button] [button link=”http://blog.exodusintel.com/2015/08/13/stagefright-mission-accomplished/” icon=”fa-external-link” side=”left” target=”blank” color=”285b5e” textcolor=”ffffff”]Source: Exodus[/button]Last Updated on November 27, 2018.










