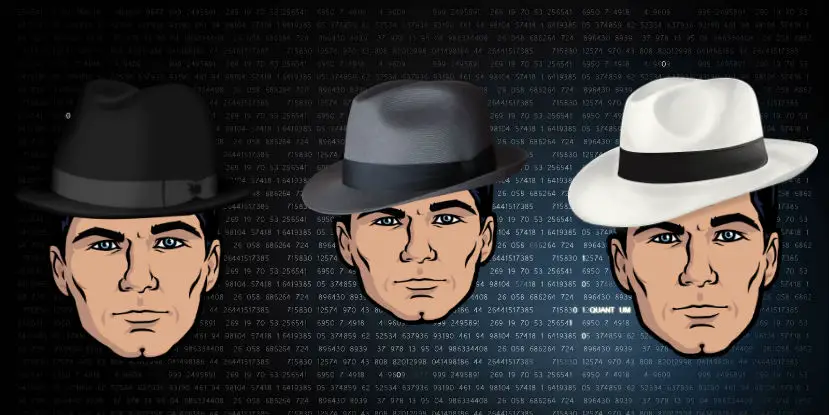
The Short Guide To Hacker Hat Colors
Hackers. The name given to those who can break into computer systems and manipulate it for their own nefarious reasons, usually financial in nature. Day after day we hear the news talk about the latest hack, Target, US Postal Service, IRS, Albertson’s and the list goes on. But this is only what you see reported in the mainstream media. The media rarely tells you that the hackers who took control of a Jeep were not up to no good. No. These were hackers that were trying to make a product better by finding vulnerabilities before anyone else did and let the company know so they could fix it. In this short guide, we’ll look at the three different color “hats” hackers wear.
Black Hat Hackers
These are the ones you hear about most often, why? Because they cause the most damage and the media is all about reporting damage and who caused the damage. Black Hat hackers will hit systems to find whatever exploit or vulnerability they can find to seize control of their target system. Sometimes they will hold the systems hostage for a ransom fee. Sometimes they will collect data and make other demands beyond monetary (see Ashley Madison hack). Sometimes they will collect data and logs to sell them to a third-party to manipulate and use. Overall these are the bad guys, they’re in it for personal gain or to cause as much damage as they can, just because they can.
White Hat Hackers
These are the ones you hear about breaking into car systems but the media rarely explains they’re the good hackers. White hats generally look for exploits in computer systems (with permission) then report their findings to the company whom they’ve exploited, allowing the company to patch that system. Often times companies will hire white hats to test their systems to be sure there wasn’t anything missed in production. Often times white hats earn their living doing this work for companies. It’s invaluable to the companies to have someone who has the abilities of the black hats but with good moral character. Sometimes companies put out a bounty for white hats to attempt to break into systems, it’s part of the companies research and development. Overall these guys want to do good and want everyone to be safe.
Grey Hat Hackers
There’s always blurred lines in life and that’s where the Grey Hat hackers fall in. While not as destructive as black hats the grey hats will sometimes commit illegal activities without consent from the company and then report the flaw or vulnerability. Sometimes the grey hats will break into systems just for fun and not inform anyone of the flaws. Sometimes they’ll find holes in systems and make them public without informing the target company. The grey hat doesn’t usually commit any crimes with their activities (which can be crimes in themselves) but they don’t always follow proper methods of finding flaws. Overall the grey hats are more curious than anything, in their own world not really caring if what they do is legal or illegal.
Conclusion
Whenever you watch your next local newscast remember, the reporters reporting the story are more than likely less tech savvy than you. Often times their reports cast a dark shadow around all hackers when this isn’t the case at all. We covered three different types of hackers in this short guide but there are other hackers we didn’t cover. Some are hackers who like to hack their smartphones and tablets to run custom ROM’s. These are hobbyist hackers who usually contain their activities within their own world. So remember, not all hackers are bad, like any battle of good and evil you need a good guy and bad guy and that’s exactly what we have in cyber-warfare.
feature image contains the character Archer from FX and is property of FX networks
Last Updated on November 27, 2018.










Comments are closed.