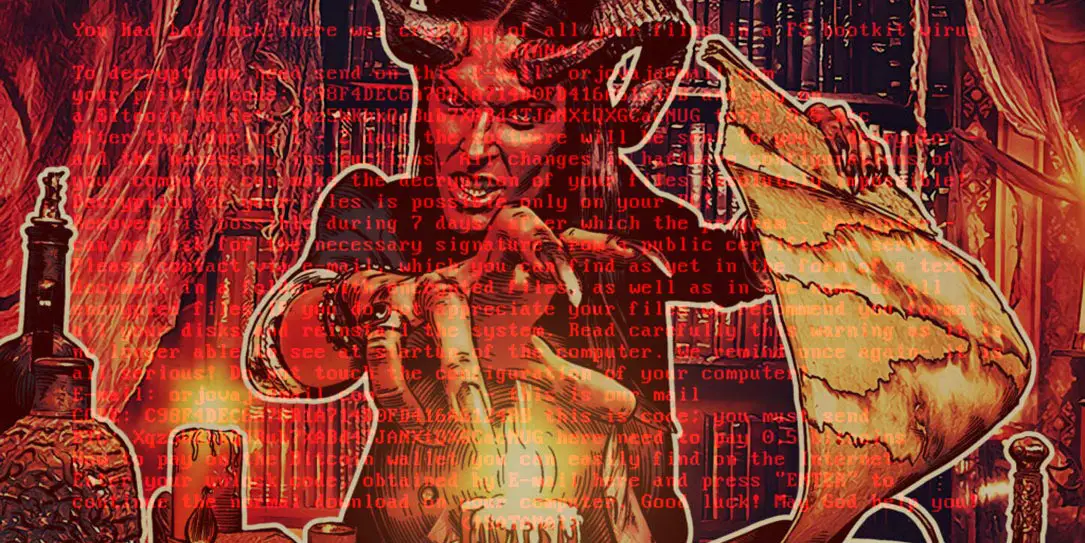
Viruses and malware are becoming more sophisticated as time goes on. One of the more notorious viruses is the Petya ransomware which corrupts a Windows computer’s Master Boot Record (MBR). If the MBR is corrupted, the computer can’t boot. Petya then used a second Trojan to encrypt PC files. A new ransomware — dubbed Satana (or “Satan”) — takes Petya one step further and not only corrupts the MBR but also encrypts files on the PC, holding them hostage until a Bitcoin ransom is paid.
Once it’s inside the system, Satana scans all drives and network instances, looking for .bak, .doc, .jpg, .jpe, .txt, .tex, .dbf, .db, .xls, .cry, .xml, .vsd, .pdf, .csv, .bmp, .tif, .1cd, .tax, .gif, .gbr, .png, .mdb, .mdf, .sdf, .dwg, .dxf, .dgn, .stl, .gho, .v2i, .3ds, .ma, .ppt, .acc, .vpd, .odt, .ods, .rar, .zip, .7z, .cpp, .pas, and .asm files, and starts encrypting them. It also adds an e-mail address and three underscore symbols to the beginning of the file name (for example, test.jpg would become Sarah_G@ausi.com___test.jpg).
The e-mail addresses are meant to serve as contact information for the victims, who are supposed to write to the address to get payment instructions and then retrieve the decryption key. So far, researches have seen six e-mail addresses used in this campaign.
Once infected, a ransom demand of 0.5 Bitcoins (roughly $340USD) is demanded to decrypt the affected files and restore the MBR. Kaspersky reports that there is a way that the MBR can be fixed, however once it’s restored the issue of the encrypted files remains. As of yet there is no fix available for the encrypted files.
Kaspersky Lab has a few tips for how you can protect yourself against ransomware.
10 tips to protect your files from ransomware https://t.co/o0IpUU9CHb #iteducation pic.twitter.com/I47sPIiWFF
— Kaspersky Lab (@kaspersky) November 30, 2015
Have you been hit by ransomware? What steps do you take to prevent from getting infected? Let us know in the comments below, or on Google+, Twitter, or Facebook.
[button link=”https://blog.kaspersky.co.uk/satana-ransomware/7413/” icon=”fa-external-link” side=”left” target=”blank” color=”285b5e” textcolor=”ffffff”]Source: Kaspersky Lab[/button]