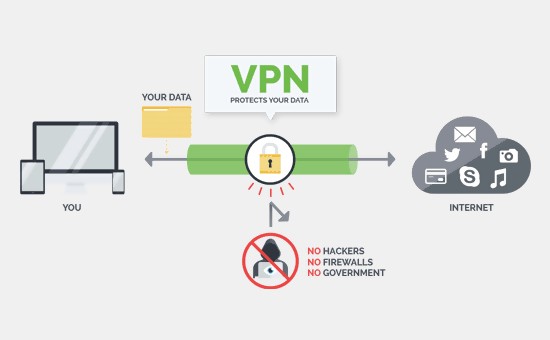
VPN is an acronym for Virtual Private Network, a network which gives individuals and businesses access to the internet through a confidential channel by transmitting their internet traffic through a software program. This network encodes certain documents through its software while it attempts to anonymously connect the user to the internet. When you start using VPN, hidden documents pass through the VPN for prompt, safe message delivery without interference. Therefore, documents receivers see the incoming directory is protected without specific information of any given geographical area.
In this brief article explanation, the word code will be used in some context to represent protocols in most cases while explaining the operations of Virtual Private Network systems.
VPN Protection
VPNs are an important tool for business users who travel and need to connect to their work network. Using a VPN can protect transmitted data and user credentials. Businesses generally use VPNs designed specifically for business users. As a matter of fact, some businesses will not allow connection to its internal network from outside unless it’s through their provided VPN with authentication.
Consumers can benefit from these protections when using consumer-level VPNs on public or guest Wi-Fi connections. Using a VPN can help protect their data better than using an open Wi-Fi connection.
Guarantee of VPN performance raises dispute amid tech professionals specifically in the IT business where there is competition, innovation, and new development. Although there is a policy which raises issues around the constitutional and policy control of VPNs, these controls have not decreased the activities around its mechanization in its newly developed data encryption.
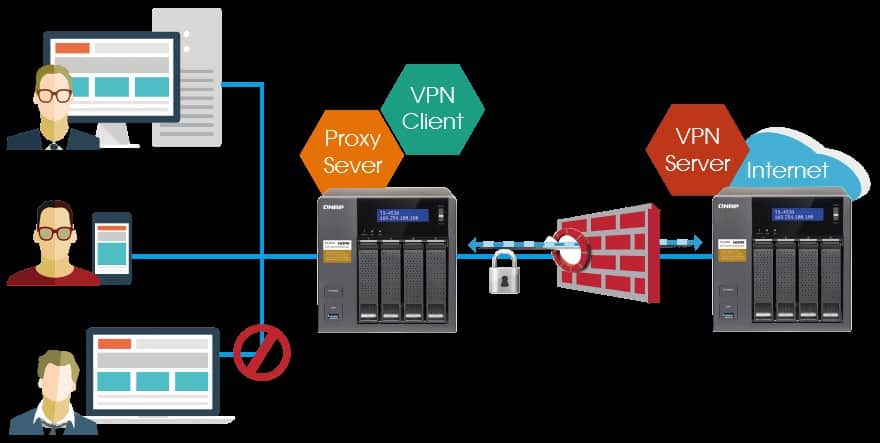
VPN Protocols
The protocols of VPNs define how the service handles the transmission of data over the VPN server. The prevalent systems operated by most users include:
- Secure Socket Tunneling Protocol: The system is a Microsoft-created protocol with a network ingrained with some SSL/TLS encoding. The strength is structured on similar-key cryptography; a setup discreet to a limited individual who has the ability to decode the document sent and received.
- Point To Point Tunneling Protocol: is obviously the most aged code basically produced. It is a first-generation code that operates with an operating system which is easy to install. Although, the connection is barely secure.
- L2TP/IPsec (Layer 2 Tunneling Protocol): is a merger of PPTP with Cisco’s L2F protocol and operational employing keys to start up a personalized safe net establishment by the sender or receiver but barely safe in terms of its execution which can be easily broken by some agencies.
- IKEv2 Internet Key Exchange, Version 2: equips individuals and developers with arguably one of the most outstanding safety net built by Microsoft.
- OpenVPN: doesn’t have the flaws which the other systems listed above do. It’s positioned on SSL/TLS and the project is open that is the project gives an opportunity to frequent innovation, development, and upgrades by the hi-tech group. The OpenVPN protect the network by operational codes strictly privatized by the two individuals who chose to use it. In fact, it’s an adaptable, resourceful and the most secure code.
Is VPN Expensive?
The average cost out of widely known VPNs is US$5.00 a month and about US$149.99 annually. Investing US$5 a month in a VPN can often pay off, especially if you’re using public Wi-Fi or Wi-Fi networks you may not be familiar with. A VPN can help protect your privacy and keep you secure. There are some Virtual Private Network providers who offer discounts and price breaks for signing up. It’s also important to remember that you can cancel at any time and switch VPNs if you find a better deal. Most of these providers do not lock you into a subscription.
Last Updated on February 3, 2021.











Comments are closed.