The adoption of container technologies, DevOps principles and practices, and Kubernetes to orchestrate it all, are three of today’s most critical tech revolutions driving modern digital business transformation. More and more companies are looking to divest from their on-premises data centers and instead either migrate their existing monolithic apps to a containerized environment in the cloud or build their mission-critical applications in the cloud using container and Kubernetes technology—also known as cloud-native application development.
Even companies born in the cloud era see the importance of using the right combination of technologies to build their applications in the most scalable manner. Tinder recently announced their move to Kubernetes. Soon after, Twitter announced its own migration from Mesos to Kubernetes. While the reasons behind such rapid adoption of Kubernetes has been well documented, security issues remain one of the biggest concerns for organizations. When your container and Kubernetes security becomes an afterthought, it’s not uncommon to find yourself in the headlines for all the wrong reasons—just ask Tesla.

To better understand the state of container and Kubernetes security and adoption, we conducted a survey of over 200 IT and security decision-makers in November of 2018. We recently repeated the survey across nearly 400 individuals in Security, DevOps, and Product teams to gain additional insights into how organizations are adopting container technologies and how their security concerns have evolved. The key findings centered around the rapid adoption of Kubernetes as the default orchestrator, security once again topping the list of container strategy concerns, and organizations more often choosing a hybrid environment over cloud-only or on-prem-only infrastructure to run containerized applications.
The results are in close alignment with the prediction from Gartner that by 2022 more than 75% of global organizations will be running containerized applications in production – a significant increase from fewer than 30% today.
Kubernetes adoption increases at a blistering rate
Originally developed by Google—based on their learnings from the Borg and Omega projects—Kubernetes was open-sourced in 2014 as a platform for automating deployment, scaling, and management of containerized applications. Google partnered with the Linux Foundation to form the Cloud Native Computing Foundation (CNCF) to manage the Kubernetes open-source project.
By 2017, cloud behemoths AWS and Azure were announcing their own versions of managed Kubernetes services. Microsoft announced the planned release of Azure Kubernetes Service (AKS) and AWS followed suit a month later with the announcement of Amazon Elastic Container Service for Kubernetes (EKS).
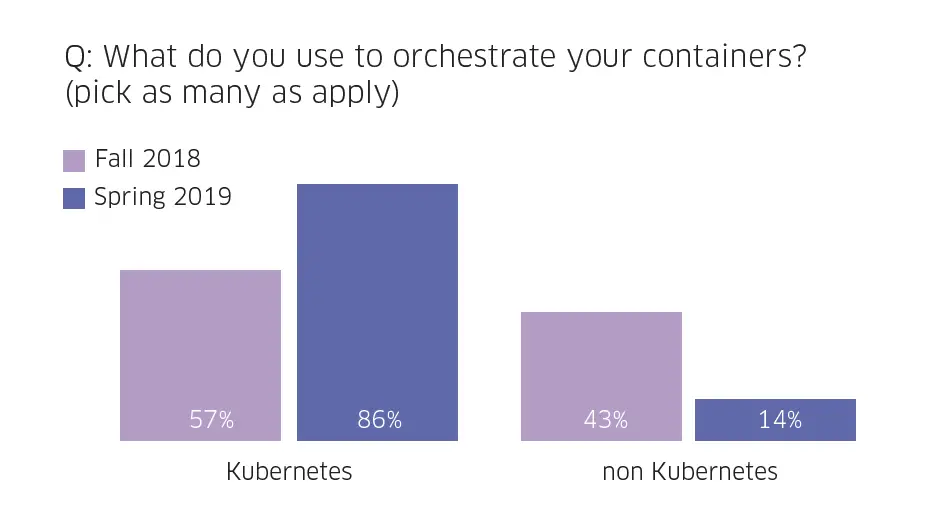
Since then, Kubernetes usage has taken off. In our original survey conducted in November of 2018 57% of respondents said they used Kubernetes to orchestrate their containers which were already larger than any other orchestrator in the market. When we conducted the survey again in July 2019, the percentage of survey respondents using Kubernetes grew dramatically, from 57% to 86% – a 50% increase.
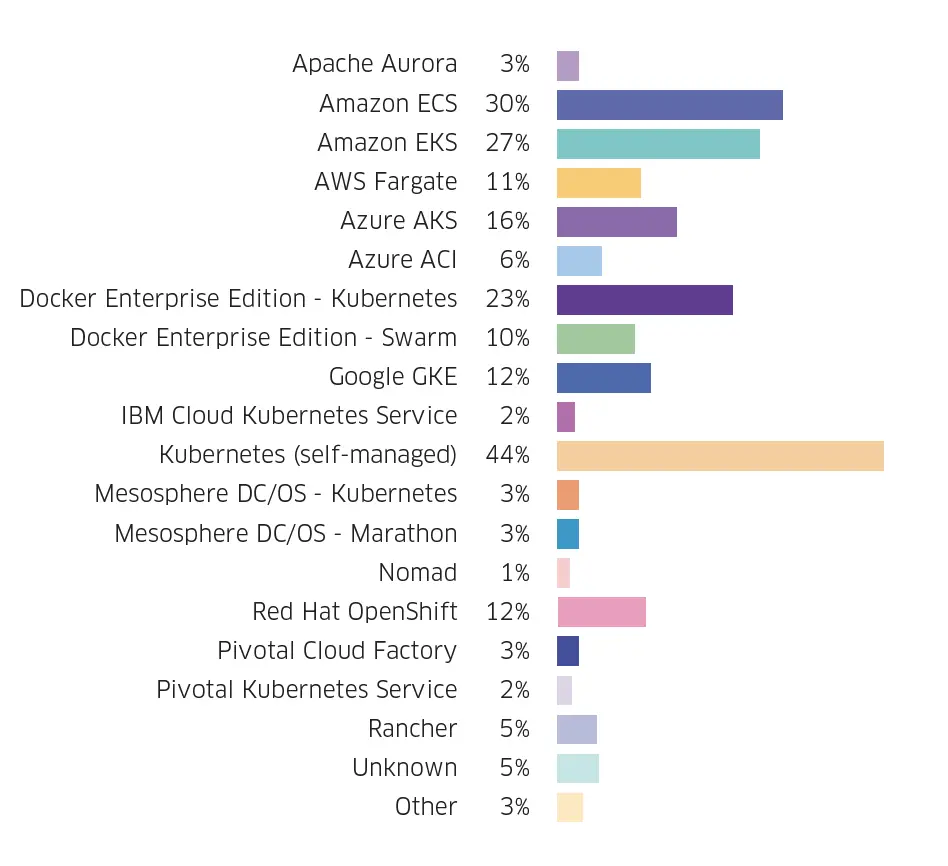
And while all major cloud providers offer their own managed Kubernetes service (which is supposed to be easier to use) a large portion of Kubernetes users self-manage their Kubernetes clusters. This is likely because it gives organizations additional flexibility to easily port their Kubernetes applications to another environment.
Survey respondents report increasing concerns for container and Kubernetes security
Security concerns remain one of the leading constraints for using containers and Kubernetes. 2019 saw the discovery of several high-severity containers and Kubernetes vulnerabilities, including the runC vuln, a k8s privilege escalation flaw, a DoS vuln, and several other vulns that were announced in August 2019 as part a CNCF audit.
Most respondents pointed to inadequate investment in security as their biggest about their company’s container strategy. The list of the container and Kubernetes security considerations is numerous, and existing security tooling isn’t suitable to address them. Organizations need dedicated security controls purpose-built for containers, Kubernetes, and microservices, to meet their security and compliance obligations. For example, unlike traditional waterfall method of application development, modern app dev methodologies rely on continuous integration and continuous delivery (CI/CD) where security controls must be deeply embedded in the CI/CD pipeline for it to be effective.
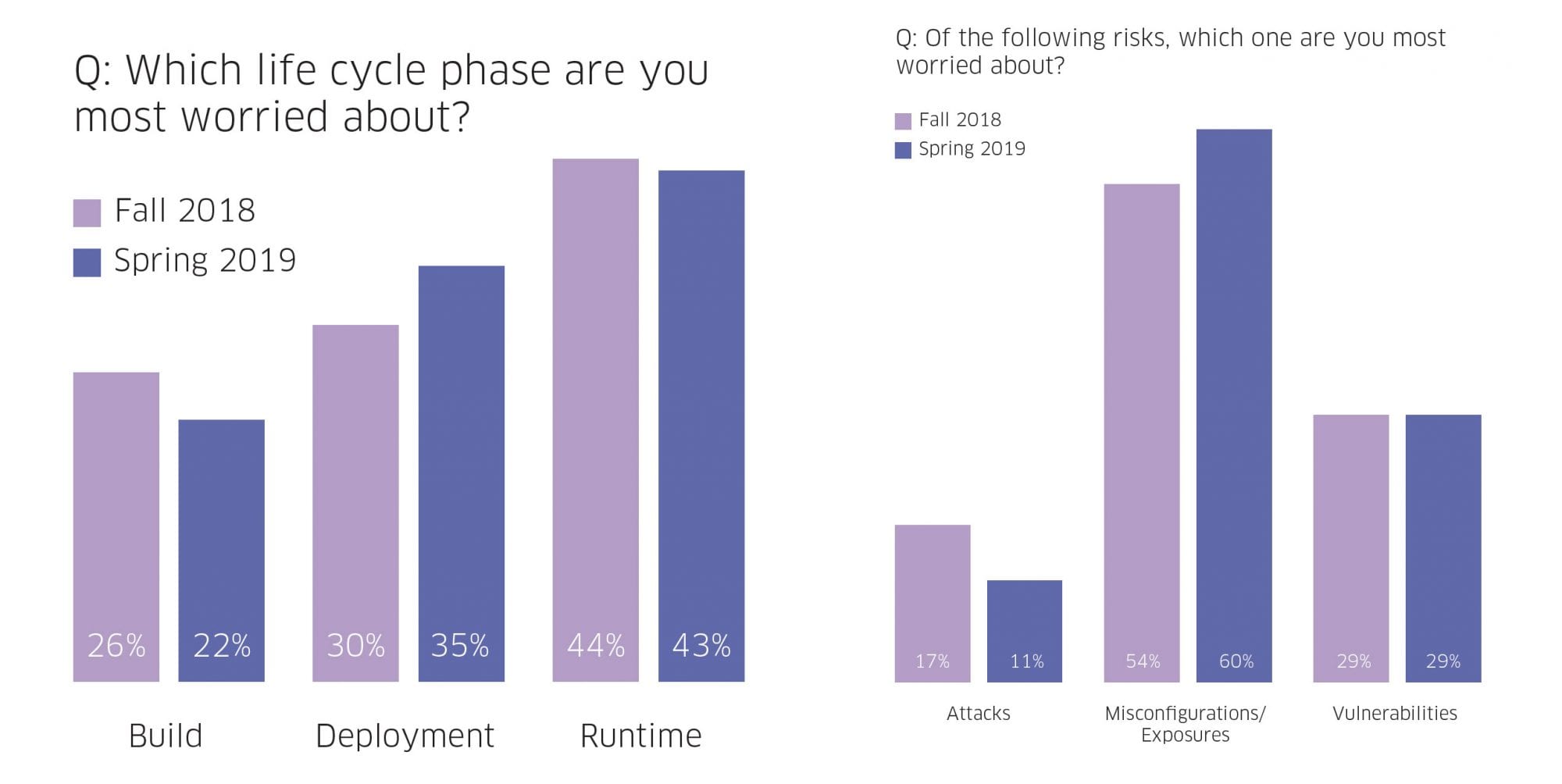
Runtime continues to be the container life cycle phase that organizations are most worried about; however, most organizations realize that runtime failures are a function of missed security best practices during the build and deploy phases. For that reason, more than half (57%) of respondents are more worried about what happens during the Build and Deploy phases. In other words, users realize they must “shift left” in their application of security best practices to build it right the first time.
Containers are running everywhere
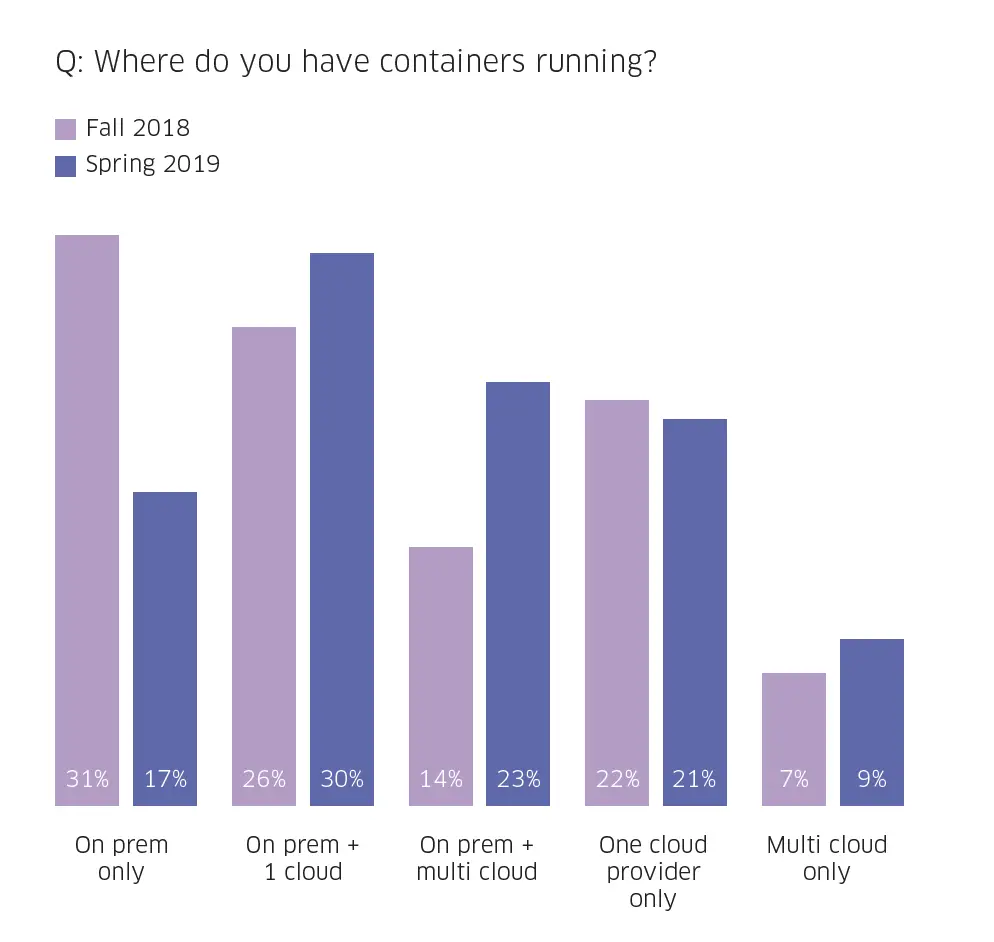
70% of respondents are running containers on-prem, but 75% of those running on-prem are also running them in the cloud, which means that any workable security solution has to span both environments.
Today, more than half of respondents (53%) are running in hybrid mode compared to 40% at the end of 2018. Conversely, the percentage of organizations running containers only on-premises has dropped nearly in half (from 31% to just 17%), while cloud-only deployments have remained steady.
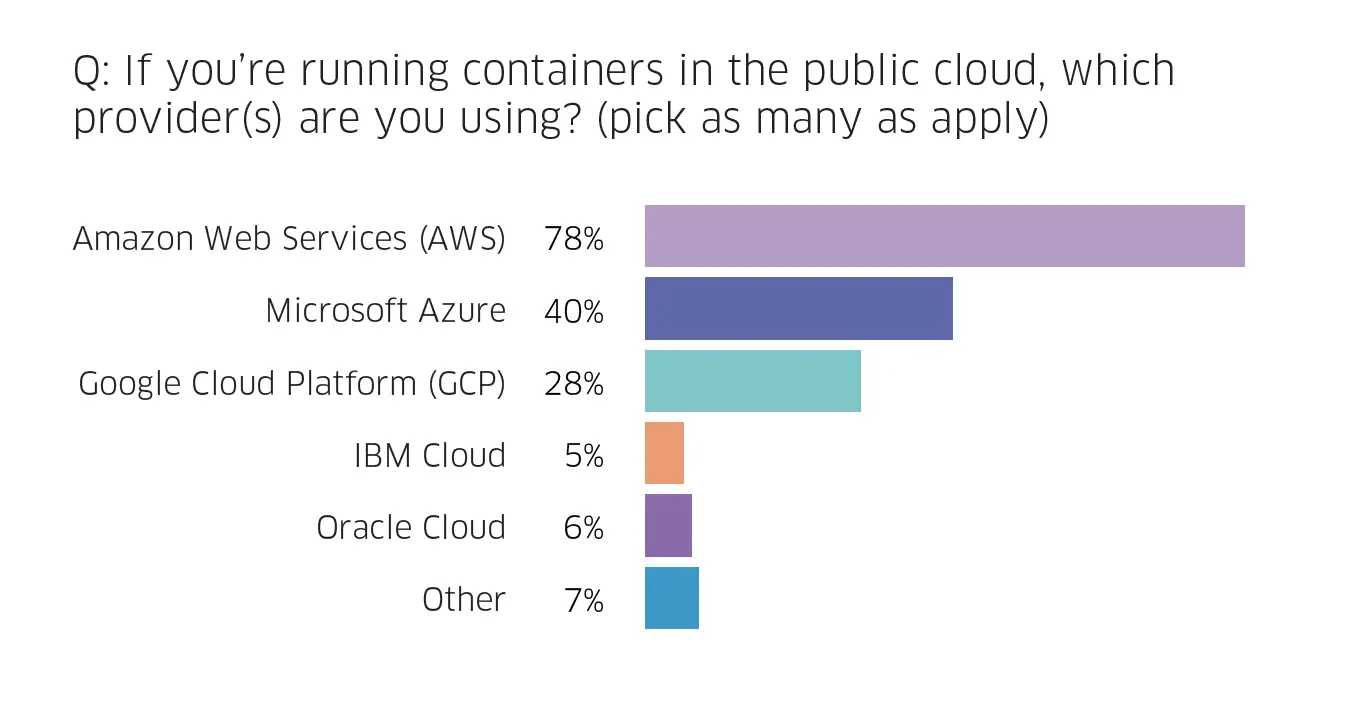
To no one’s surprise, AWS continues its market dominance in container deployments, followed by Azure. Google comes in third, and it has gained considerable market share, growing from 18% to 28% over six months.
The rise of DevSecOps
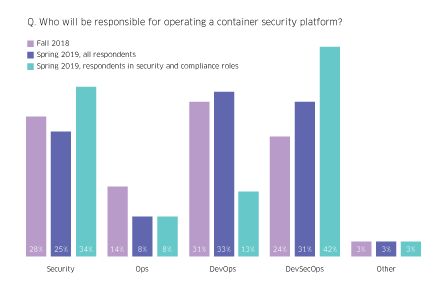
The increasing complexity of security threats facing enterprises is leading to the DevSecOps role taking on increasing prominence in managing container security. Across all operations roles, the allocation of management responsibility by role remained consistent, but the jump in those citing DevSecOps as the responsible operator for container security is significant. When analyzing only those survey respondents who are in a security or compliance role, there is an even larger jump in the allocation of responsibility to DevSecOps – 42% of respondents in a security or compliance role view DevSecOps as the right organization to run container security programs.
Conclusions
While container security is still a significant concern, containerization is here to stay. The benefits of leveraging containers and Kubernetes—allowing development teams to move fast, deploy software efficiently, and operate at an unprecedented scale—is clearly outpacing the anxiety of security vulnerabilities.
Organizations have far more containers running in production than just six months ago. The percentage of organizations with more than 50% of their containers running in production has increased from 13% to 22% – a growth rate of 70%. In the same six months, those running less than 10% of their containers in production has fallen from 52% to 39%.
Organizations can’t afford to treat security as an afterthought. Unlocking the benefits of cloud-native technologies while maintaining strong security for mission-critical application development infrastructure requires protecting the full container life cycle – across build, deploy and runtime phases.
This guest post was written by Ali Golshan, StackRox CTO
“With a passion for building disruptive products, Ali is Co-founder and CTO for StackRox, where he oversees the company’s technology strategy and roadmap. Prior to StackRox, Ali was the Founder & CTO of Cyphort (acquired by Juniper Networks) and led the company’s product strategy and research initiatives.”
Last Updated on February 3, 2021.