This guest post was written by Erich Kron, his full bio can be found following this article.
An interesting thing happened to me at the car dealership today. I had to take my car in for service and after dropping it off with the service folks, I settled into the waiting area and set up my little remote working space. Now, this was not a small shop or tiny dealership, this was a pretty major BMW dealership in the area. In other words, it had a nice on-demand coffee machine complete with cappuccino settings, free sodas, and waters, etc. as you would expect in a luxury dealership used to dealing with high-value customers (myself excluded). So what about free Wi-Fi?
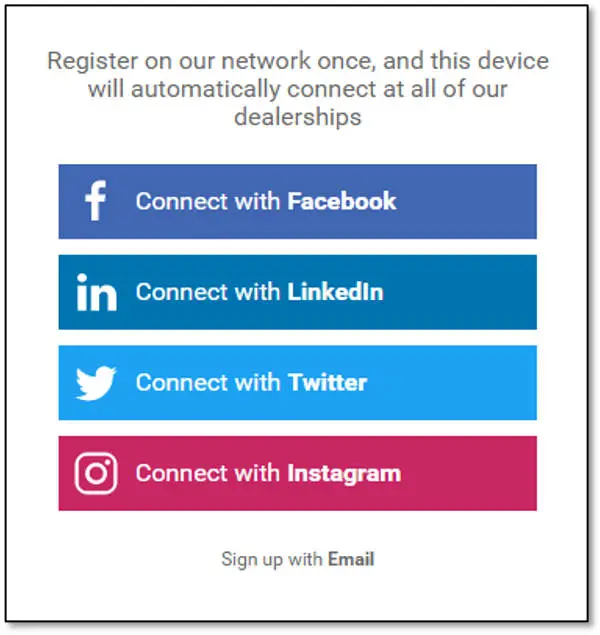
Well of course it had was a free Wi-Fi network for guests. No real surprise there as people are used to having to wait in places like this and not having a free Wi-Fi connection would be, well, uncivilized. As I prepared to tackle more work from this little office away from the office, I connected to this free Wi-Fi network and was greeted not with the expected “Terms and Conditions” checkbox to accept in order to get on the internet, but rather a pretty involved captive portal.
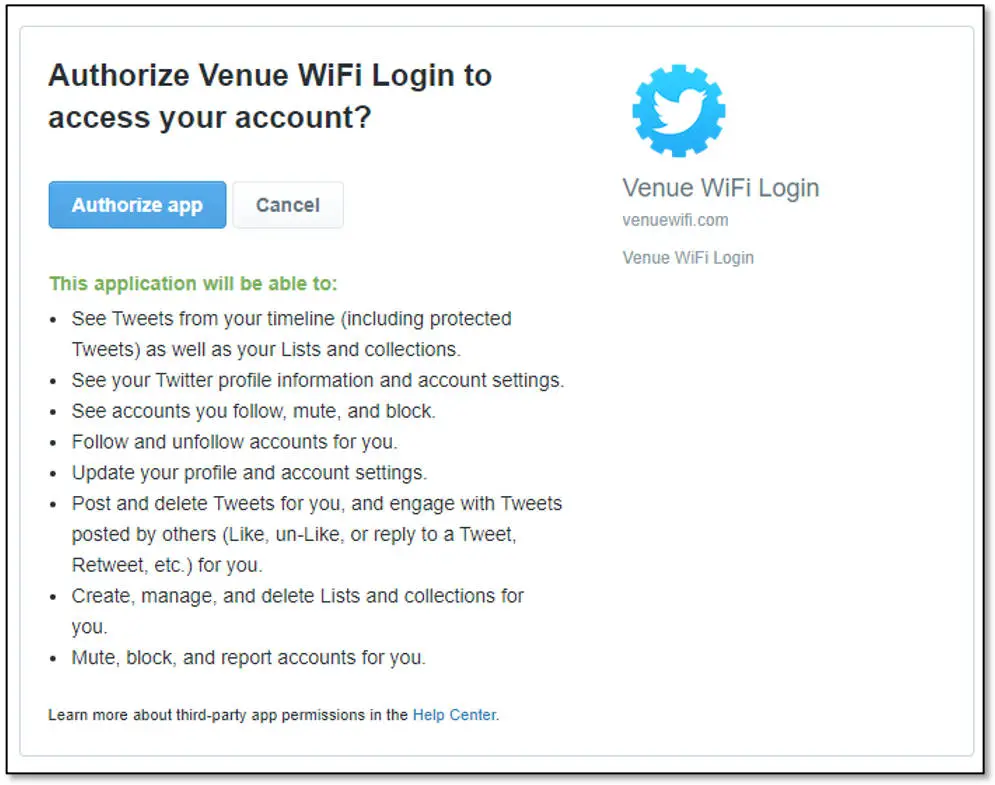
I’ve seen plenty of these Wi-Fi activation pages that request an email address, and I can even live with that, but to me, this was a whole different ball of wax. This portal was prominently asking me to use a social media platform as an authentication provider. OK, this also is not new in some cases, however, I am used to seeing this used for different services on the web, not usually for free Wi-Fi access. This got me curious, so in the interest of security I chose the button to use Twitter as a provider and as expected, was served a screen asking me to authorize the app to allow me to log in.
This is where I was a little surprised. Not only was the app requesting rights to see my profile, but also to do things like post and delete tweets for me, update my profile and account settings and even follow and unfollow accounts for me. All of this so I can get on the free Wi-Fi at the dealership.
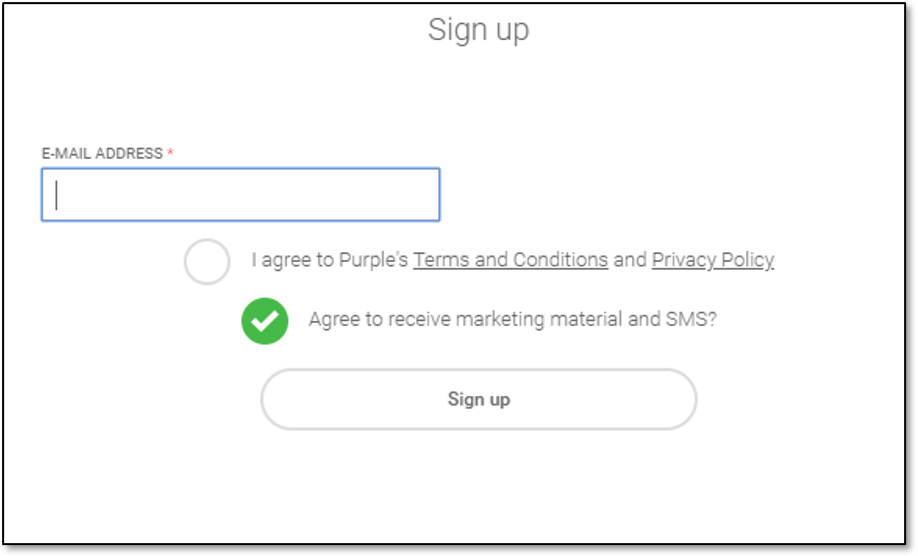
Remember, this is a high-end BMW dealership, which tends to attract some high-end clientele and it is asking for some serious access to social media accounts. In the end, I chose the option to log in via email. I expect I will be contacted by the organization, however since I already purchased a car there, it is information they already have.
This is a stark reminder of the importance of teaching people how to look at something like this and see the risk. Executives and celebrities are often already familiar with looking at risk at a corporate level, but also must be aware of the risks at a personal level. Accepting these permissions could put social media accounts at risk, especially if they use personal accounts such as Facebook. In addition, if these types of authentication requests become the norm, attackers could use weaponized versions of these types of pages to steal credentials from unsuspecting users.
Organizations employing this sort of technology should consider the risks they are imparting on their customers as well. I recognize that while some of these services are offered for ‘free’ to the organization deploying them, the real cost comes from their customers in the way of their privacy and security.
Requesting an email address in exchange for Wi-Fi is reasonable, however, requesting access such as this is simply taking it too far. Please read these types of things before accepting and, whenever possible, chose not to use them or only provide the most basic information. Free Wi-Fi is not worth giving your private data, or control over your data to anyone.
What do you think? Would you grant access to your social media account for free Wi-Fi? Let us know in the comments below or on Twitter, Facebook, or MeWe.
About the Author: Erich Kron, Security Awareness Advocate at KnowBe4, is a veteran information security professional with over 20 years’ experience in the medical, aerospace manufacturing and defense fields. He is the former security manager for the US Army’s 2nd Regional Cyber Center-Western Hemisphere and holds CISSP, CISSP-ISSAP, MCITP and ITIL v3 certifications, among others. Erich has worked with information security professionals around the world to provide the tools, training and educational opportunities to succeed in Information Security.
In some of our articles and especially in our reviews, you will find Amazon or other affiliate links. As Amazon Associates, we earn from qualifying purchases. Any other purchases you make through these links often result in a small amount being earned for the site and/or our writers. Techaeris often covers brand press releases. Doing this does not constitute an endorsement of any product or service by Techaeris. We provide the press release information for our audience to be informed and make their own decision on a purchase or not. Only our reviews are an endorsement or lack thereof. For more information, you can read our full disclaimer.
Last Updated on February 3, 2021.