AirDrop is by far the easiest method to share files between Mac, iPhone, and iPad out there today. AirDrop not only lets you share files between your own devices in a snap, but you can share with others around you that have AirDrop turned on. But you’d probably be interested to know that Apple’s wireless file-sharing system has had a security flaw since 2019, and Apple has not acknowledged or addressed it.
Estimated reading time: 3 minutes
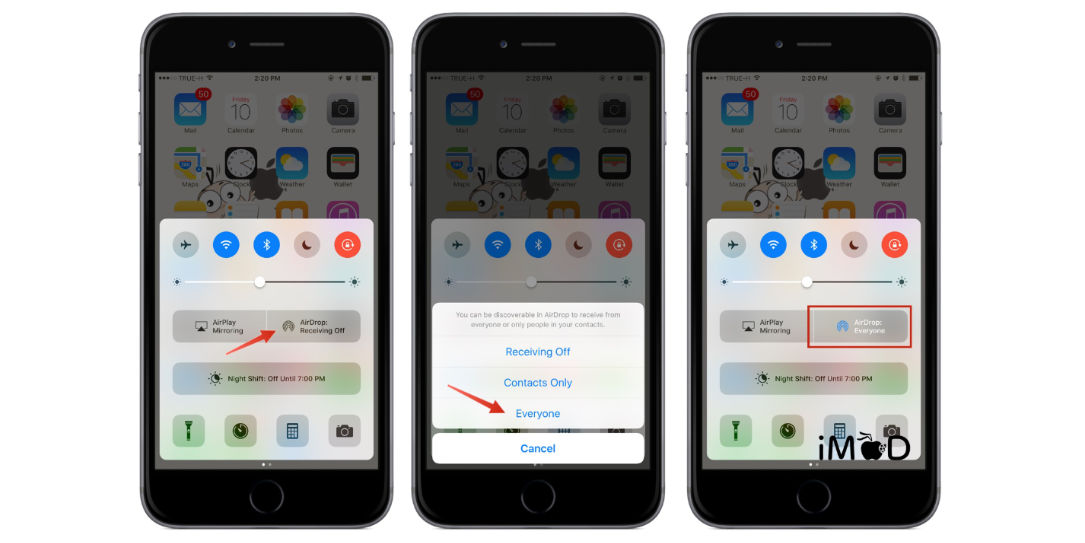
What’s worse is, there are no available fixes for the security flaw, and the only way to protect against it is to turn AirDrop off. The technology uses WiFi and Bluetooth to connect to nearby devices allowing the sharing of files between devices. The folks over at Ars Technica have an excellent explanation of how things work here.

To determine if the device of a would-be sender should connect with other nearby devices, AirDrop broadcasts Bluetooth advertisements that contain a partial cryptographic hash of the sender’s phone number and email address. If any of the truncated hashes matches any phone number or email address in the address book of the receiving device or the device is set to receive from everyone, the two devices will engage in a mutual authentication handshake over Wi-Fi. During the handshake, the devices exchange the full SHA-256 hashes of the owners’ phone numbers and email addresses.
Hashes, of course, can’t be converted back into the cleartext that generated them, but depending on the amount of entropy or randomness in the cleartext, they are often possible to figure out. Hackers do this by performing a “brute-force attack,” which throws huge numbers of guesses and waits for the one that generates the sought-after hash. The less the entropy in the cleartext, the easier it is to guess or crack, since there are fewer possible candidates for an attacker to try.
The amount of entropy in a phone number is so minimal that this cracking process is trivial since it takes milliseconds to look up a hash in a precomputed database containing results for all possible phone numbers in the world. While many email addresses have more entropy, they too can be cracked using the billions of email addresses that have appeared in database breaches over the past 20 years.
“This is an important finding since it enables attackers to get hold of rather personal information of Apple users that in later steps can be abused for spear phishing attacks, scams, etc. or simply being sold,” said Christian Weinert, one of the researchers at Germany’s Technical University of Darmstadt who found the vulnerabilities. “Who doesn’t want to directly message, say, Donald Trump on WhatsApp? All attackers need is a Wi-Fi-enabled device in proximity of their victim.”
Ars Technica
The researchers who discovered this AirDrop flaw say they notified Apple in 2019 and even developed an alternative that is more secure and presented it to Apple. But Apple has been silent on the matter. Apple generally keeps its mouth shut regarding security flaws and anything that may give the company a bad look. So it will be interesting to see if they finally acknowledge this flaw or not.
In the meantime, if you’re concerned about security using AirDrop, the best thing to do is turn it off and only use it when needed and in a place you know there aren’t others around who shouldn’t be receiving your transmissions.
What do you think of this security flaw in AirDrop? Please share your thoughts on any of our social media pages. You can also comment on our MeWe page by joining the MeWe social network.